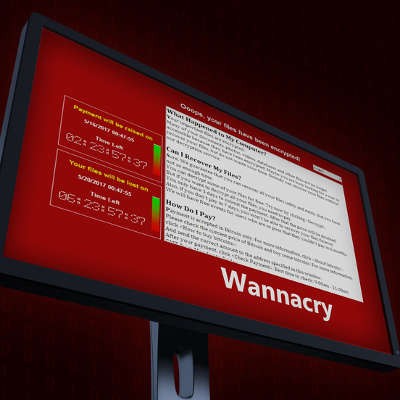
On May 11th, 2017, the world was introduced to the WannaCry ransomware. The ransomware spread around the globe like wildfire, infecting hundreds of thousands of devices and catching many major organizations and businesses by surprise. The full extent of the ransomware’s damage is still being assessed, yet, one thing we do know: this whole fiasco was preventable.
The Connection, Inc Blog
The Connection, Inc has been serving the New Jersey area since 1992, providing IT Support such as technical helpdesk support, computer support and consulting to small and medium-sized businesses.
0 Comments