The Connection, Inc Blog
For small businesses with limited budgets and workforces, getting the type of maintenance needed to keep complicated pieces of machinery and technology in tip-top shape seems like a tall order. Sometimes it might be a budgetary issue, where it costs too much to hire in-house staff to handle this burden. Other times it might seem like you just can’t find any talent in your location. Thanks to modern technology—remote monitoring and management technology, in particular—you are no longer stuck by these limitations
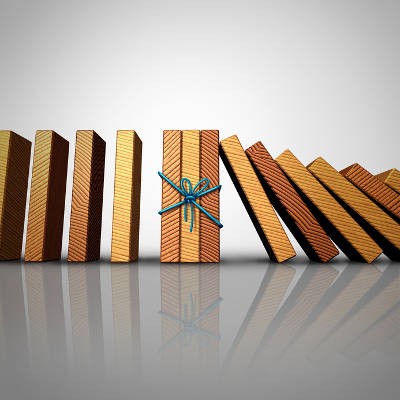
More small businesses today depend on their IT. If that technology isn’t working as intended, it can really stymie an organization’s ability to be effective. Our strategy of managed IT support and services can do quite a bit towards keeping a business running efficiently. Today, we’ll take a look at managed IT to see how proactive monitoring can deliver enhanced efficiency to businesses.
Every business has some sort of management tasks that requires foresight, and staying up on them can keep headache-inducing situations from constantly causing downtime and costing you time; and, make no mistake, time is money. Being more proactive not only provides sound strategies, it can really mitigate the amount of problems you have to deal with. As we describe what it means to be proactive, and how that strategy will almost always help you save money, consider how you are implementing a proactive approach to your business.
News & Updates
Understanding IT
Get the Knowledge You Need to Make IT Decisions
Technology is constantly evolving, and keeping up can feel overwhelming. Whether you want to understand cybersecurity threats, explore automation, or learn how regulations like PCI DSS impact your business, we’ve made it easy to access clear, straightforward insights on key IT topics.
Contact Us
Learn more about what The Connection can do for your business.
The Connection
51 Village CT
Hazlet, New Jersey 07730