The Connection, Inc Blog
A lot of people never stop and consider how their data is saved. It’s something we all have, from old photos of our family vacations to the files kept on the server back at the office, but not many people know the actual mechanics behind it. Today, we wanted to go over these specifics, and hopefully make it clear why we always advocate for backup practices.
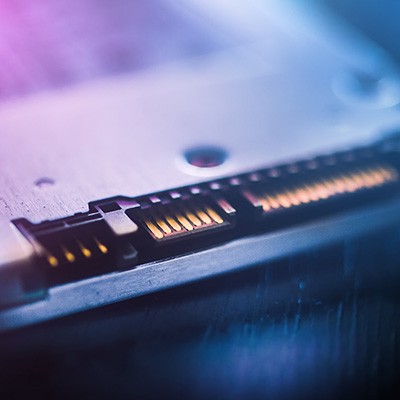
How does your business handle its on-premise, physical data backups? This is a question that you don’t necessarily have to ask yourself under pressure of a looming data loss incident. Despite the cloud being the clear victor in terms of restoration and reliability, physical data backup is still an important part of the business continuity process. In the worst-case scenario, a physical backup can be helpful for getting back on track.
Few things are more frustrating and annoying than a slow computer. There are a lot of things that can slow a computer down, too: viruses and malware, excess applications running in the background, even time can seem to turn a relatively fast computer into a slow-as-molasses impediment to productivity.
If your computer is overall healthy but starting to slow down, there is one simple upgrade that can make a whole world of difference.
News & Updates
Understanding IT
Get the Knowledge You Need to Make IT Decisions
Technology is constantly evolving, and keeping up can feel overwhelming. Whether you want to understand cybersecurity threats, explore automation, or learn how regulations like PCI DSS impact your business, we’ve made it easy to access clear, straightforward insights on key IT topics.
Contact Us
Learn more about what The Connection can do for your business.
The Connection
51 Village CT
Hazlet, New Jersey 07730