The Connection, Inc Blog
Technology is increasingly important for business, which is why when making decisions about what technology to use and how to use it, decision makers need all the information they can get. Since businesses today depend more on software than ever, it is extremely important that you know why it is so important to keep your business’ applications updated and patched.
For the small business, technology is an issue; and reasonably so. For something that holds so much importance for an organization, there are bound to be problems attached. These problems can disrupt efficient workflows and ruin some situations. In this week’s blog, we will take a look at four things you can do to cut down on your technology troubles.
Even the solutions designed to keep businesses and organizations safe are vulnerable to the threat of a cyberattack, as when it all boils down, these tools are still software solutions, no matter how secure they might be. The company in question today—Barracuda—is a huge name in the cybersecurity industry, and it has become the victim of a zero-day exploit. Let’s go over how you can prevent your business from experiencing the same thing.
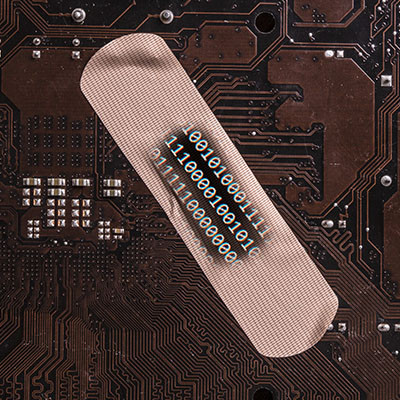
It’s easy to use the terms “patches” and “updates” as if they mean the same thing, and they are often used interchangeably within the same context. However, understanding the difference between the two can make a world of difference in terms of how you approach implementing each of them. We’re here to clear things up a bit and help you better understand the patches and updates you deploy on a month-to-month basis.
We live in a world of the “as a service” business model, where services are rendered on a per-month or per-billing cycle service model rather than the traditional “buy now, replace later” one. What they don’t tell you, however, is that when you use Software as a Service (SaaS) for multiple purposes, things can get messy pretty quickly. How do you manage all of your software solutions without breaking the bank (and your brain)?
Software runs our lives. It certainly runs your business. What if I told you that this essential cog in your business’ operations can also be the thing that is most susceptible to being exposed by outside attackers? It’s true, software can be the very door that hackers and scammers need to get into your network and run amok. Let’s take a look at the unsung service that is patch management and why it is so important.
August saw yet another Patch Tuesday designed to resolve security issues in Microsoft products. Out of the 48 vulnerabilities resolved, 15 affected Windows, while 25 were rated as critical, 21 as important, and 27 that allowed for remote code execution. This might sound a little overwhelming, so we’ll try to simplify it a bit--a lot of flaws were fixed, and the majority of them can be considered dangerous for your organization.
It’s imperative that your organization’s software is managed properly. If you can’t do this, then your operations can suffer in the long run. While this might sound like a lot of work, software management isn’t as difficult as it sounds if you break it down into compartmentalized tasks. Ultimately, you can group it into three major steps: leveraging available assets, testing strategies, and understanding the software.
News & Updates
Understanding IT
Get the Knowledge You Need to Make IT Decisions
Technology is constantly evolving, and keeping up can feel overwhelming. Whether you want to understand cybersecurity threats, explore automation, or learn how regulations like PCI DSS impact your business, we’ve made it easy to access clear, straightforward insights on key IT topics.
Contact Us
Learn more about what The Connection can do for your business.
The Connection
51 Village CT
Hazlet, New Jersey 07730